Today’s article is going to be a detailed guide on how to Bypass MediaTek SP Flash Tool SLA DAA Authentication. For those worried, if they will have to visit the Service centers in order to get their device unbricked, hold on. The solution is here. Simply follow the easy step-by-step process and you will be able to use SP Flash tool without asking for any permissions.
If you have a MediaTek device and you are skeptical about whether or not you can customize it like any Qualcomm device, then let me break it to you. Yes, you can. Thanks to the SP Flash tool that allows users to flash MediaTek devices using the SP Flash tool and unbrick MediaTek devices using the SP Flash tool.
However, the picture has changed a bit now. Earlier users could use SP Flash tool in order to use the Download Mode for MediaTek devices to flash and unbrick their devices. Yes, they can do it using the Fastboot commands too but not for hard-bricked devices.
Since the low-level Download mode could access the entire device storage, OEMs like Xiaomi and Realme have now introduced a way to complicate the flashing process – SLA and DAA. The Serial Link and Download Agent authentication require users to take permission to unbrick or flash their device from the Customer service centers.
Now, this is an issue for our tech enthusiasts. However, what you can do is Bypass SP Flash Tool SLA DAA Authentication for MTK phones. To know how, scroll down!
What is SP Flash Tool’s SLA and DAA Authentication for MediaTek devices?
SLA stands for Serial Link Authentication and DAA stands for Download Agent Authentication on SP Flash Tool. These two, as their names suggest are authentication identifying checks. This will authorize only those people to carry out flashing using SP Flash tool who have Serial Link and Download agent programs. Which further points towards Service center employees.
So in this way, you will be left with no choice but to visit the nearest service center and get your device unbricked or flashed. Quite inconvenient, right? Well not anymore, the guide below will help you in bypassing MediaTek SP Flash tool SLA and DAA authentication.
What is SP Flash Tool?
SP Flash tool is a tool from MediaTek that can be used to update or download firmware on MediaTek Android devices. You can read our comprehensive guide on the SP Flash tool here. This amazing tool can basically help you in resetting and fixing a bricked device. Other perks of this one include the ability to test device memory.
However, now the picture seems to have changed a little. In order to prevent users from using the SP tool to flash firmware and unbrick devices, the OEMs have added SLA and DAA authentication. Which means one will have to take prior permission in order to flash or unbrick their device.
However, the reason I mentioned the change as a “little” one is that we can now bypass SP Flash tool SLA and DAA Authentication for Mediatek devices using a simple process. All thanks to senior XDA developers – Dinolek and k4y0z.
Keep reading further to know more about how to bypass SP Flash tool authentication for SLA and DAA.
How to Bypass MediaTek SP Flash Tool SLA DAA Authentication
Given below is a detailed guide on how to bypass MediaTek SP Flash Tool SLA DAA Authentication.
Just note that –
- www.androidjungles.com will not be responsible for any (if any) damaged that has been caused to your device using the below guide. This guide is for knowledge purposes only.
- Go through the below-mentioned supported MediaTek chipsets to avoid any mishap on your device.
Supported MediaTek Chipsets
Here is a list of the Supported MediaTek Chipsets that are compatible with the procedure given below. Check first that your phone comes in the list mentioned below and only then proceed further. If your device does not fall in the below-supported category then we would recommend you to abstain from the procedure.
Do not worry if your device chipset is not supported here, chances are that it will be added in the near future. So you can bookmark this page and visit later to check.
mt6261 mt6572 mt6580 mt6582 mt6735 mt6737 mt6739 mt6755 mt6757 mt6761 mt6763 mt6765 mt6768 mt6771 mt6785 mt6799 mt6873 mt8127 mt8163 mt8173 mt8695
For ease of understanding and carrying out the process, we have mentioned a detailed step-by-step guide below. Make sure that you follow the steps as mentioned (numerically) for a smooth process.
Bypass MediaTek SP Flash Tool SLA DAA Authentication
Step 1. Install SP Flash Tool
Since we have to bypass SP Flash tool, it is quite obvious that we will first need to have our SP Flash tool on the PC.
- Download SP Flash Tool.
- Extract this file on any location on your PC.
Step 2. Install Python on PC
- Go to the official Python website and install Python on your PC.
- (Make sure that you download Python from the official site only to avoid any further issues.)
- Now, double click on the Python EXE File so as to set it up.
- Next, from the bottom of the menu, Click on Add Python to Path option.
-

Bypass SP Flash Tool authentication via python unbrick Xiaomi - Click on Install now if you want to install it on the default location. I would recommend you installing Python on the default location.
- However, you can also choose the path to install Python using the option of Customize Install.
- The below will be the path if you choose the default directory.
C:\Users\UserName\AppData\Local\Programs\Python\Python39
- Make sure to remember this location as we will be needing it in the further step.
Step 3. Install Python Dependencies
If you are wondering why we have to install Python dependencies, then this is to prevent library version conflicts.
- Go to the installation directory.
- In the address bar, type cmd.
- A command prompt will launch on the Window.
- Now enter the below command in the command prompt and hit the enter key. You can also copy-paste it for your convenience.
-
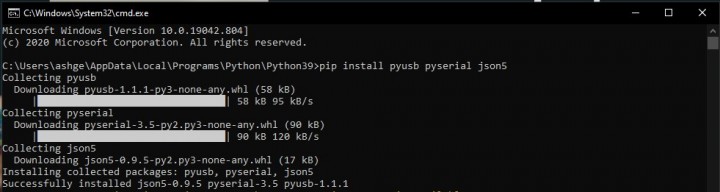
install python pyusb json5
pip install pyusb pyserial json5
- Now that you have installed the needed Python Dependencies, you can proceed further.
Step 4. Install libusb-win32
For those wondering, libusb win-32 is a port of the USB library libusb – 0.1. This is required as we will need a specially tweaked USB Driver so as to intercept the exploit payloads and bypass SP Flash Tool authentication.
- Hoping that you have understood its necessity, download libusb-win32 on your PC.
- Now double click on the libusb-win32-devel-filter-1.2.6.0 file so as to open and set it up.
- Next, to get done with the installation of this USB driver, simply follow the instructions given on the screen.
-
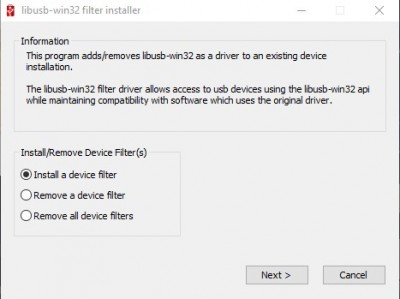
lib USB win 32 setup bypass MediaTek SP Flash Tool SLA and DAA Authentication;
Step 5. Download MTK Bypass Utility tool
I am assuming the name itself would be helping you out the importance of using this tool and its work in our bypassing SP Flash tool process.
- Download MediaTek Bypass tool.
- Extract the file on any location on your PC as per your wish.
-
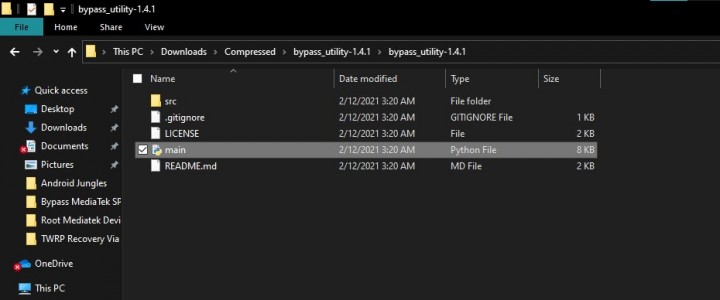
MediaTek bypass utility tool bypass SP Flash Tool SLA and DAA Authentication; - Next, you will have to move all these files to the Python installation directory.
Step 6. Boot MediaTek device into Download Mode
Similar to Qualcomm’s Emergency Download Mode, we have a Download mode on for MediaTek devices which can be used to unbrick MediaTek device. If we have to bypass SP Flash tool SLA and DAA Authentication, entering the Download Mode is essential. Here is how you can enter into Download Mode –
- Switch off your device.
- Press the Volume Up button. However, if you have a Xiaomi device, press the Volume Down button.
- While pressing the button, simultaneously connect your device to the PC using the USB Cable.
- You will enter into Download Mode on the MediaTek device.
Step 7. Bypassing SP Flash Tool SLA DAA Authentication
Now comes the most important part. However, before proceeding further, Make sure that you have followed all the prior steps and have carefully followed each and every process.
- Go to the folder where you have saved the Python file. You can refer to step 2 for this process.
- In this folder, type cmd in the address bar.
-
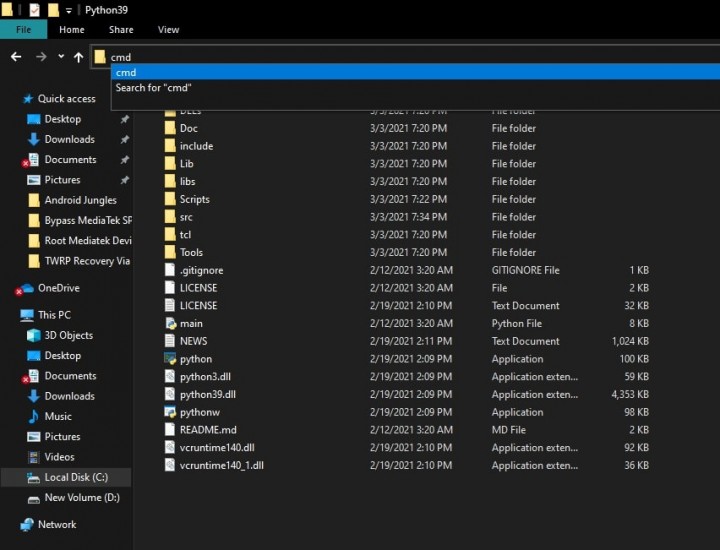
python cmd window - This will open a Command prompt inside the Python directory.
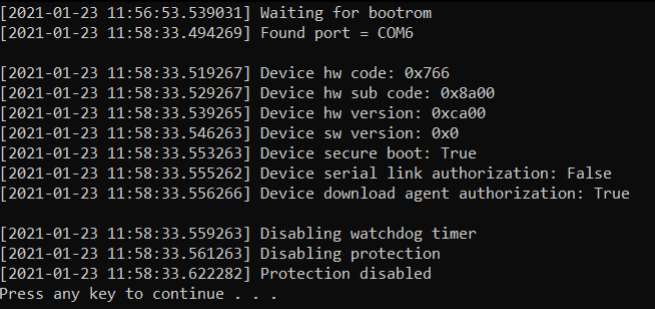
- Enter the below command so as to run main.py python file –
-
MediaTek-SP-Flash-Tool-SLA-DAA-Authentication-Bypass;
python main.py
- Once entered, you will now get a message on the screen asking – “Protection Disabled, Press any key to continue”.
- Open SP Flash Tool. For this, you can double-click on the flash_tool.exe file.
- In the tool, go to Options and choose Connection.
- Then, under the Connection Settings, choose UART.
-
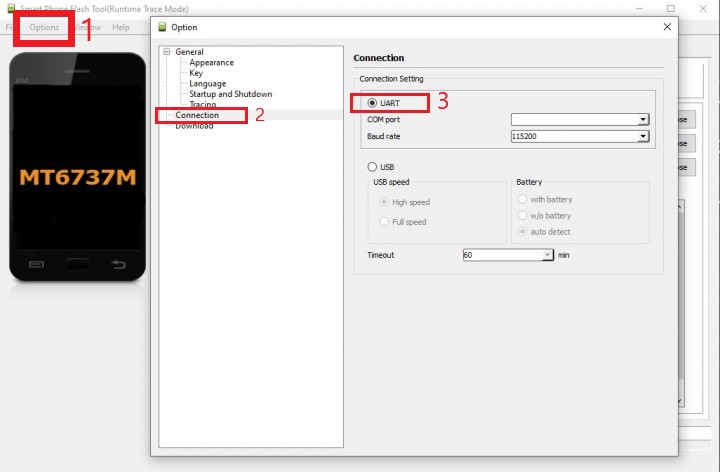
sp flash tool uart connection
That is it. You can now flash the firmware you wish as you have successfully bypass Serial Link Authentication and Download Agent Authentication on the SP Flash Tool. You will not need to worry about any authentication or permissions to ask before you flash or unbrick your MTK device.
Concluding Words
Thanks to XDA Developers Dinolek and k4y0z who possess all the credits for the tweaks and the entire process. That was all about Bypassing MediaTek SP Flash Tool SLA DAA Authentication. Serial Link and Download Agent authentications have to be bypassed in order to flash firmware using SP Flash tool or Unbrick Mediatek device using SP Flash tool.
In case you are stuck at any of the above steps, feel free to let us know in the comment section below. We will get back to you as soon as possible.
Happy Androiding:-)